Serverless compute plane networking
This page introduces tools to secure network access between the compute resources in the Databricks serverless compute plane and customer resources.
To learn more about the control plane and the serverless compute plane, see Network reference architecture overview.
To learn more about classic compute and serverless compute, see Compute.
Databricks charges for networking costs when serverless workloads connect to customer resources, and when performance-intensive services egress data cross-region back to clients. See Understand Databricks networking costs.
Serverless compute plane networking overview
Serverless compute resources run in the serverless compute plane, which is managed by Databricks. Account admins can configure secure connectivity between the serverless compute plane and their resources. This network connection is labeled as 2 on the diagram below:
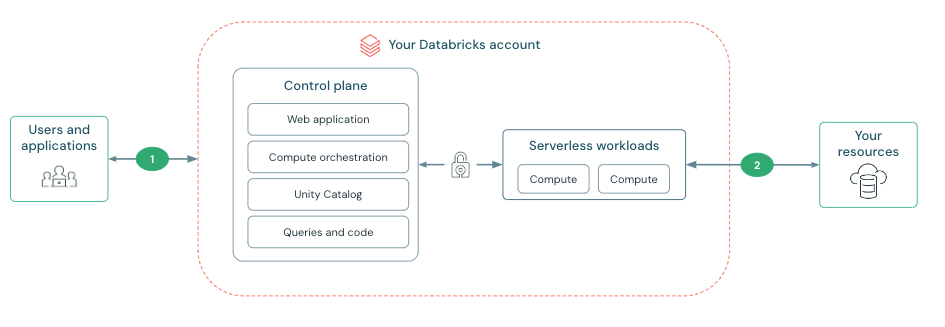
Connectivity between the control plane and the serverless compute plane is always over the cloud network backbone and not the public internet. For more information on configuring security features on the other network connections in the diagram, see Networking.
Data transfer costs
Serverless compute plane networking products might incur data transfer costs. For detailed information on data transfer pricing and types of data transfer, see the Data transfer and connectivity. To avoid cross-region charges, Databricks recommends you create a workspace in the same region as your resources.
Databricks private connectivity enables secure connections to cloud resources without public IP addresses. When using private connectivity with serverless workloads customers are charged per hour for each private endpoint and per GB for data processed through these endpoints.
Features using Databricks private connectivity are in private preview, contact your Databricks account team for access.
What is a network connectivity configuration (NCC)?
Serverless network connectivity is managed with network connectivity configurations (NCCs). NCCs are account-level regional constructs that manage private endpoint creation.
If you use stable IPs from the legacy Public Preview or copied them from a network connectivity configuration (NCC) in the account console, you must migrate to the new method before May 25, 2026. See Outbound IPs for workspaces enabled for serverless firewall preview.
After May 25, 2026, the legacy list of IPs is decommissioned and is no longer available through the NCC UI or Network Connectivity API. Workloads relying on legacy allowlists might experience connection errors.
Account admins create NCCs in the account console and an NCC can be attached to one or more workspaces to enable firewalls for resources. See Serverless compute firewall configuration.
Creating a resource firewall also affects connectivity from the classic compute plane. You must also allowlist the networks on your resource firewalls for connections from classic compute resources.
NCC firewall enablement isn't supported for Amazon DynamoDB. When reading or writing to DynamoDB in the same region as your workspace, serverless compute resources use direct access through AWS gateway endpoints.
Databricks uses S3 gateway endpoints, private IPs, and public IPs to connect to resources based on their location and type. These connectivity methods are generally available unless explicitly stated otherwise.