Manage IP access lists
This page introduces IP access lists for the Databricks account and workspaces.
IP access lists overview
This feature requires the Enterprise pricing tier.
IP access lists enhance security by providing control over which networks can connect to your Databricks account and workspaces. The default allows connections from any IP address.
- Restrict access based on the user's source IP address.
- Allow connections only from approved networks like corporate offices or VPNs.
- Block access attempts from insecure or public networks like coffee shops.
There are two IP access list features:
- IP access lists for the account console: Account admins can configure IP access lists for the account console to allow users to connect to the account console UI and account-level REST APIs only through a set of approved IP addresses. Account admins can use an account console UI or a REST API to configure allowed and blocked IP addresses and subnets. See Configure IP access lists for the account console.
- IP access lists for workspaces: Workspace admins can configure IP access lists for Databricks workspaces to allow users to connect to the workspace or workspace-level APIs only through a set of approved IP addresses. Workspace admins use a REST API to configure allowed and blocked IP addresses and subnets. See Configure IP access lists for workspaces.
If you use PrivateLink, IP access lists apply only to requests over the internet (public IP addresses). Private IP addresses from PrivateLink traffic cannot be blocked by IP access lists. To block specific private IP addresses from PrivateLink traffic, use AWS Network Firewall. If you want to restrict the PrivateLink connection to a set of registered PrivateLink endpoints, change your workspace's private access settings object to use the ENDPOINT access level. See Configure classic private connectivity to Databricks.
Context-based ingress controls
This feature is in Public Preview.
While IP access lists filter requests based only on source IP addresses, context-based ingress controls let account admins combine multiple conditions—such as user identity, request type, and network source—into allow and deny rules. These policies provide more granular control over who can reach your workspace and from where.
Context-based ingress control is configured at the account level. A single policy can govern multiple workspaces, ensuring consistent enforcement across your organization.
Both controls apply together. A request must be allowed by the account-level context-based ingress policy and by any workspace IP access lists. Context-based ingress can restrict access based on identity or request scope, and IP access lists can restrict access based on network location. If either control blocks the request, access is denied.
See Context-based ingress control.
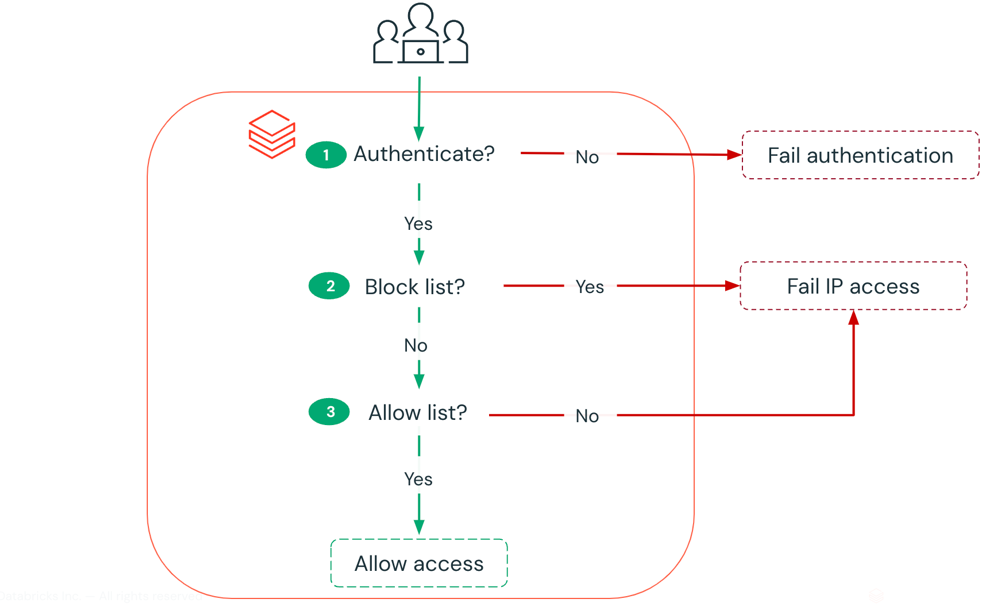
How is access checked?
The IP access lists feature allows you to configure allow lists and block lists for the Databricks account console and workspaces:
- Allow lists contain the set of IP addresses on the public internet that are allowed access. Allow multiple IP addresses explicitly or as entire subnets (for example
216.58.195.78/28). - Block lists contain the IP addresses or subnets to block, even if they are included in the allow list. You might use this feature if an allowed IP address range includes a smaller range of infrastructure IP addresses that in practice are outside the actual secure network perimeter.
When a connection is attempted:
- First all block lists are checked. If the connection IP address matches any block list, the connection is rejected.
- If the connection was not rejected by block lists, the IP address is compared with the allow lists. If there is at least one allow list, the connection is allowed only if the IP address matches an allow list. If there are no allow lists, all IP addresses are allowed.
If the feature is disabled, all access is allowed to your account or workspace.
For all allow lists and block lists combined, the account console supports a maximum of 1000 IP/CIDR values, where one CIDR counts as a single value.
Changes to IP access lists can take a few minutes to take effect.
Next steps
- Configure IP access lists for the account console: Set up IP restrictions for account console access to control which networks can access account-level settings and APIs. See Configure IP access lists for the account console.
- Configure IP access lists for workspaces: Implement IP restrictions for workspace access to control which networks can connect to your Databricks workspaces. See Configure IP access lists for workspaces.
- Configure private connectivity: Use PrivateLink to establish secure and isolated access to AWS services from your virtual network, bypassing the public internet. See Configure classic private connectivity to Databricks.